In today’s hyperconnected digital environment, traditional security models are no longer sufficient to protect enterprise systems. Implementing Zero Trust Architecture for Enterprise Security is becoming essential in this landscape. With the rise of cloud computing, remote work, mobile devices, and sophisticated cyberattacks, organizations face an expanding attack surface that cannot be secured by perimeter-based defenses alone.
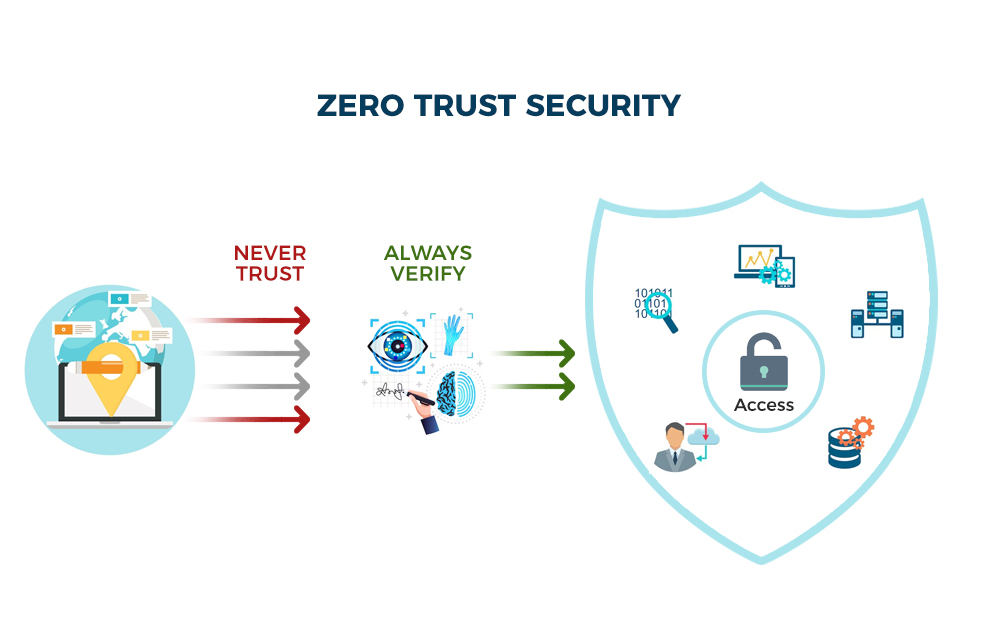
This is where Zero Trust Architecture (ZTA) emerges as a transformative cybersecurity model. Built on the principle of “never trust, always verify,” Zero Trust assumes that threats can exist both inside and outside the network, fundamentally changing how organizations manage identity, access, and data protection.
This article provides a comprehensive, research-driven exploration of Zero Trust Architecture, including its principles, components, real-world applications, case studies, benefits, challenges, and future evolution in enterprise security.
Zero Trust Architecture is a cybersecurity framework that eliminates implicit trust within an organization’s network. Instead of assuming that users or devices inside the network are safe, every access request is continuously verified.
The concept was popularized by cybersecurity analyst John Kindervag in 2010 and has since become a cornerstone of modern enterprise security strategies.
The foundational idea is simple yet powerful:
This approach drastically reduces the risk of lateral movement by attackers within a compromised network.
Traditional cybersecurity models rely on a “castle-and-moat” approach, where everything inside the network is trusted once a user gains access. However, this model is increasingly outdated.
According to cybersecurity reports, over 80% of data breaches involve compromised credentials, highlighting the weaknesses of perimeter-based security models.
Zero Trust is built on several interconnected principles that work together to create a robust security framework.
Every access request is authenticated using multiple data points, including:
Users are granted only the minimum level of access necessary to perform their tasks.
Zero Trust operates under the assumption that breaches are inevitable or already present.
Implementing Zero Trust requires a combination of technologies and policies working together.
IAM is the foundation of Zero Trust. It ensures that only verified users and devices can access resources.
Micro-segmentation divides networks into smaller zones to prevent lateral movement of attackers.
All devices accessing the network must meet strict security standards.
Zero Trust relies heavily on real-time monitoring and AI-driven analytics to detect anomalies.
When a user attempts to access a corporate resource, Zero Trust follows a strict verification process.
Many global organizations have adopted Zero Trust to strengthen their cybersecurity posture.
Google is one of the earliest adopters of Zero Trust principles through its BeyondCorp initiative.
Microsoft has fully integrated Zero Trust across its cloud and enterprise ecosystem.
Banks and financial institutions have rapidly adopted Zero Trust due to high-risk environments.
Zero Trust provides multiple advantages over traditional security models.
Despite its advantages, implementing Zero Trust is complex and resource-intensive.
Organizations must carefully plan their transition to avoid operational disruptions.
Cloud computing and Zero Trust are highly complementary. As enterprises migrate to cloud environments, Zero Trust provides a scalable security framework.
Cybersecurity trends strongly support the adoption of Zero Trust architecture:
These statistics demonstrate why organizations are shifting toward more resilient security models.
Zero Trust is expected to become the global standard for enterprise cybersecurity.
As cyber threats evolve, Zero Trust will continue to adapt and expand across industries.
Organizations planning to implement Zero Trust should follow structured best practices.
Zero Trust Architecture represents a fundamental shift in how enterprises approach cybersecurity. By eliminating implicit trust and continuously verifying every access request, organizations can significantly reduce their exposure to modern cyber threats.
As digital transformation accelerates and cyberattacks become more sophisticated, Zero Trust is no longer optional—it is essential. From cloud environments and remote workforces to critical infrastructure and financial systems, Zero Trust provides a scalable, adaptive, and resilient security framework.
Although implementation can be complex, the long-term benefits in security, visibility, and operational resilience far outweigh the challenges.